Axians Cyber Security weltweit
Axians ist ein Schweizer Service Provider im Bereich Cyber Security mit einem globalen Netzwerk von über 1000 IT- und OT-Sicherheits-Experten:innen. Kunden aus Privatwirtschaft und öffentlicher Hand vertrauen uns täglich ihre IT- und OT-Infrastruktur an. Wir unterstützen bei der Umsetzung von Sicherheits-Strategien, um Unternehmen in einer vernetzten Welt zu schützen. Von der Definition individueller IT-Sicherheitskonzepte über Managed Detection and Response (MDR) bis zur kontinuierlichen Anpassung der Strategie stehen wir Ihnen zur Seite, damit Sie sich auf den Erfolg Ihres Unternehmens konzentrieren können.

Unser IT/OT Security Operations Center
Unser ISO 27’001-zertifiziertes Security Operations Center (SOC) 24/7 bietet Ihnen die Möglichkeit, Ihre IT- und OT-Sicherheit durch Auslagerung auf ein neues Level zu heben. In Zeiten des Fachkräftemangels sichern unsere Managed Services die kontinuierliche Überwachung und den Schutz Ihrer IT- und OT-Infrastruktur. Erfahrene Sicherheitsexperten:innen erkennen Bedrohungen in Echtzeit und reagieren sofort, damit Ihr Unternehmen rund um die Uhr geschützt bleibt – proaktiv, effektiv und ohne zusätzliche Belastung Ihrer internen Ressourcen.
Unsere Leistungen
-
MEHR ERFAHREN
IT/OT Security Operations Center
Axians bietet Ihnen ein 360-Grad SOC-Service. Wir übernehmen die Planung, Implementierung, Integration in Ihre Infrastruktur sowie den 24×7 Betrieb.
-
MEHR ERFAHREN
Endpoint Security
Mit unserer Expertise für Endpoint Security sichern Sie Endgeräte und Einstiegspunkte in einer mobil geprägten Welt ab
-
MEHR ERFAHREN
Industrial IT und OT Security
Als Spezialisten im Bereich OT Security begleitet Sie Axians auf dem Weg zur Verbesserung der Cyber Sicherheit Ihrer Produktionssysteme.
-
MEHR ERFAHREN
Ransomware Readiness
Ransomware-Angriffe abwehren, auch noch nachdem alle Sicherheitsmassnahmen umgangen worden sind.
-
 MEHR ERFAHREN
MEHR ERFAHRENPentesting Services
Axians bietet eine Kombination aus manuellen und autonomen Penetrationstests, um Ihre Sicherheitslage zu analysieren und Ihre Cyber Sicherheit nachhaltig zu verbessern.
-
MEHR ERFAHREN
Security Strategy & Compliance
Axians unterstützt Sie kompetent bei der Definition und Umsetzung einer auf Sie zugeschnittenen Sicherheitsstrategie
-
MEHR ERFAHREN
Certificate Lifecycle Management
Mit einer Certificate Lifecycle Management Plattform verwalten Sie öffentliche und private digitale Zertifikate führender Zertifizierungsstellen über ein einziges Portal.
-
MEHR ERFAHREN
Network Security
Wenn hohe und zuverlässige Konnektivität für Ihren Geschäftserfolg entscheidend ist, dann muss Ihre Netzwerk Sicherheit entsprechend abgesichert sein
-
MEHR ERFAHREN
Cloud Security
Axians Cloud Security Service unterstützt Sie bei der Absicherung Ihrer Daten und Anwendungen in der Cloud
-
MEHR ERFAHREN
Identity & Access Management
MIt Identity & Access Management (IAM) behalten Sie sämtliche Identitäten und Zugriffsrechte bei einer Verwaltung im Blick
Mit uns haben Sie einen sicheren Partner an Ihrer Seite
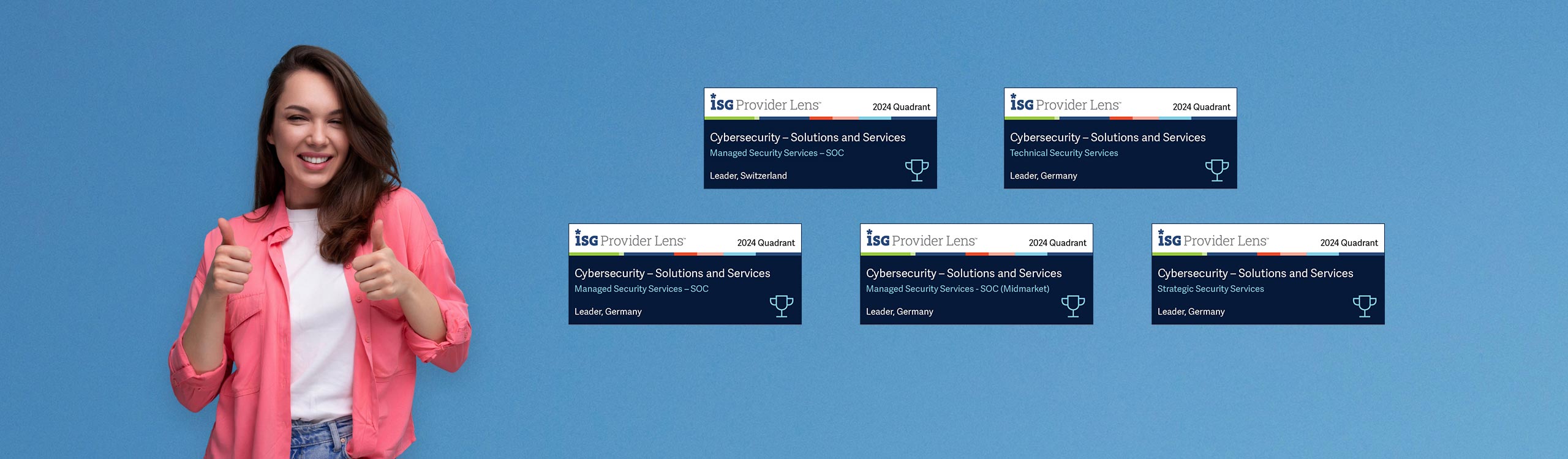
Axians Schweiz festigt führende Position im Bereich Managed Security Services
Top-Platzierung in den ISG Provider Lens™ Quadrant Studien 2024

Sie haben Fragen – unsere Cyber Security Experten_innen antworten